Tiger Research: “Korean won stablecoins need technical design beyond institutional debate”
Summary
- Tiger Research said the debate over Korean won stablecoins has been skewed toward institutional design and that technical standards for actual implementation are needed.
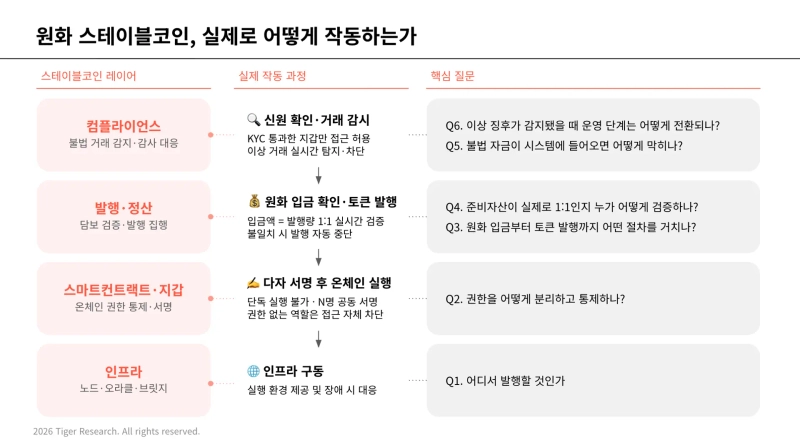
- It said six technical requirements are needed for the stable introduction of Korean won stablecoins: network architecture, permission management, issuance procedures, reserve-asset verification, anti-money-laundering and incident response systems.
- Tiger Research said that, drawing on cases such as Kaia—which has domestic financial proof-of-concept experience including the Bank of Korea’s CBDC pilot simulations—there needs to be technical discussion tied to real financial infrastructure.
Forecast Trend Report by Period

As discussion of Korean won stablecoins has centered on institutional design, an analysis says technical standards for real-world implementation are needed.
According to Tiger Research on the 2nd, from July last year to February this year, more than seven related discussions were held mainly in the National Assembly and academia. However, with the focus on institutional design—such as issuers, reserve assets and supervisory frameworks—technical discussion of how they would actually operate was found to be lacking.
Tiger Research said six technical requirements are needed for the stable rollout of Korean won stablecoins: network architecture, permission management, issuance procedures, reserve-asset verification, anti-money-laundering and incident response systems.
On network selection, it said a public L1 could be considered if the goal is rapid market entry, while a custom L2 structure could be considered if regulatory compliance and brand control are critical. For the permission model, it said role-based access control (RBAC) and a multi-signature scheme should be used to prevent unilateral execution by insiders.
It added that the issuance process should also follow a multi-step workflow—including KYC verification, confirmation of funds deposits and joint approval—and that reserve assets should be supported by a system that reconciles on-chain issuance with custodians’ balances in real time, alongside external audits.
From an anti-money-laundering perspective, it proposed a three-step response framework that moves from prior identity verification to on-chain tracing and freezing suspicious transactions. It also noted that while the issuer should bear ultimate responsibility in the event of an incident, the design should separate responsibilities by execution entity to enable post-incident response.
Tiger Research also said these technical standards need to be made more concrete based on experience integrating with actual financial infrastructure. In particular, it said the case of Kaia—which has domestic financial proof-of-concept experience such as the Bank of Korea’s CBDC pilot simulations—can serve as a reference.
Yoon Seung-sik, head of the Research Center at Tiger Research, said, “For more than a year, discussion has focused only on who will issue and what regulations will apply,” adding, “It’s time for concrete technical debate on how to build it, grounded in hands-on experience with real financial systems like Kaia.”

Suehyeon Lee
shlee@bloomingbit.ioI'm reporter Suehyeon Lee, your Web3 Moderator.